Contact Important Infomrs. Mac's Classes
- Contact Important Infomrs. Mac's Classes Nyc
- Contact Important Infomrs. Mac's Classes Near
- Contact Important Infomrs. Mac's Classes 2020
- Contact Important Infomrs. Mac's Classes Near Me
- Important: Make sure you join your meeting from the Teams desktop app (Windows or Mac) so you can create breakout rooms. When your students have joined and you are ready, select Breakout rooms from your meeting controls.
- A media access control address (MAC address) is a unique identifier assigned to a network interface controller (NIC) for use as a network address in communications within a network segment. This use is common in most IEEE 802 networking technologies, including Ethernet, Wi-Fi, and Bluetooth.
- OACES is the Office of Adult and Career Education Services, a division of the Rochester City School District www.rcsdk12.org.
The text below contains important information for grant applicants and for other parties to their grant applications. You should refer to it at each stage of your grant application. Mac android emulator multiple instances.
When you apply for a student grant, each party to your application is required to confirm that they have read and understood these important notes as terms and conditions relating to your application and to any grant awarded to you.
The Institute for Operations Research and the Management Sciences. 5521 Research Park Drive, Suite 200 Catonsville, MD 21228 USA. Phone 1 443-757-3500. Phone 2 800-4INFORMS (800-446-3676).
This document will be updated to reflect any changes in legislation and is updated on this page.
1. Legislation
The legal terms and conditions governing student grants are contained in the legislation under which SUSI operates:
- Student Support Act 2011, as amended,
- Student Grant Scheme for relevant year,
- Student Support Regulations for relevant year.
2. Grant Eligibility
The legislation sets out eligibility criteria and other conditions that determine whether you may receive a grant including –
- nationality and residency,
- previous education and grant history,
- progression in education and repeating,
- maximum periods of grant funding,
- approved institutions and courses,
- chosen institution and course,
- applicant class,
- income of parties to an application,
- income threshold limits,
- other sources of education funding,
- dependent children,
- relevant persons in education,
- distance from ordinary residence to college.
Some key criteria and conditions are highlighted below but you should also refer to the full text of the legislation provided at www.susi.ie
3. Grant Application and Decision Processes
All grant applications and supporting information and enquiries must be submitted by you, the applicant, through the official processes operated by SUSI.
SUSI will determine whether you are eligible to receive a grant, having regard to –
- information furnished by you,
- other relevant information, including information from other relevant Government bodies,
- criteria specified in the legislation.
4. Full, Complete and Accurate Information
Under the legislation, all information required by SUSI in respect of all parties to your application must be provided by you, the applicant. SUSI communicates directly with you, the applicant only, for these purposes.
SUSI will therefore request all required information from you, the applicant, only and will notify you directly in writing of its decision on your application.
All information that you provide must be full, complete and accurate in every respect. Before submitting a grant application each party to your application must make a declaration to confirm this in respect of their information.
If you fail to provide information or if you provide information that is incomplete or inaccurate this may result in the delay or refusal of your application.
Your Responsibilities
You must immediately inform SUSI if you become aware of a material change in circumstances concerning you or another party to your application that may mean any of the following:
- any information that you have provided to SUSI in your application is no longer correct, or
- any other information that you have provided to SUSI in relation to yourself or another party to your application is no longer correct, or
- you no longer comply with the criteria or conditions necessary to remain eligible for a grant.
5. Review of Eligibility
You may apply to SUSI for a review of your eligibility to receive a grant in the event of any of the following changes of circumstances occurring between 1 January of the year in which you apply for a grant and the end of the academic year to which your application relates:
- income,
- number of dependent children,
- number of relevant persons in education,
- normal place of residence,
- nationality or immigration status,
- course or institution.
SUSI may review your eligibility to receive a grant where-
- you apply for a review of your eligibility,
- you provide or fail to provide information required by SUSI,
- SUSI receives a report or other relevant information relating to your application.
Following a review of your eligibility, SUSI may determine that-
- you remain eligible for a grant,
- you are eligible for a different grant, or
- you are not eligible for a grant.
SUSI may cease grant payments while it is reviewing your eligibility to receive a grant.
6. Right of Appeal
You may appeal a decision by SUSI to award or refuse you a grant. Your appeal must be made to the SUSI Appeals Officer within 30 days of receipt of the letter notifying you of the decision. An appeal form is provided on our Appealing your Grant Decision page at www.susi.ie
7. Offences and Penalties
Where any information that you provide to SUSI includes a deliberate or reckless omission, falsehood or inaccuracy or where you fail to notify SUSI of a material change of circumstances having a bearing on your application or your grant, you may be liable to prosecution for an offence which may lead to penalties including a fine, imprisonment, or both, or to loss of grant and repayment, with interest, of any moneys received.
8. Grant Payments
Payment of any maintenance grant awarded to you can commence after your college has confirmed to SUSI that you are registered and in full time attendance on your course. This information is requested by SUSI directly from your college.
Payment of any fee grant awarded to you is made directly to your college by SUSI on your behalf on the basis of your confirmed registration and attendance.
Before you can receive maintenance grant payments, SUSI requires your bank account details. These details can be provided securely through your online SUSI account once you have been awarded a grant by SUSI.
9. Recovery of Overpayments
If, for any reason, you receive payment of some or all of a grant for which you are not eligible, you will be liable to repay to SUSI any maintenance grant paid to you and any fee grant paid to a college on your behalf.
10. Key Eligibility Criteria and Conditions
Applicant Class
If you are aged 23 years or over, you should pay particular attention to the applicant class that you select when you make your online grant application.
Please refer closely to the help notes provided in the application form and refer also to the further information provided at www.susi.ie
Each year many students who select an incorrect applicant class experience delays in the processing of their applications and are required to cancel their applications and to make a new application under the correct class.
Your Chosen Course
Grants can only be awarded in respect of approved courses as set out in the legislation.
You do not need to have accepted a place on a course in order to apply for a grant. However you will need to inform SUSI that you have been offered and accepted a place on a course before your application can be finalised. You can do this in the following ways:
- Online SUSI Grant Application: you can confirm that you have accepted a place on a course when you submit your online grant application;
- CAO Applicants: if you have allowed the CAO (Central Applications Office) to share your information with SUSI by selecting the appropriate option in your CAO application form, the CAO will inform SUSI of this and will confirm details of your course to SUSI when you have accepted a CAO place offer;
- Online SUSI Course Change Notification Form: you can inform SUSI that you have accepted a place on a course at any time after you have submitted your grant application by submitting an online Course Change Notification Form through the homepage of your online SUSI account (previously known as Final Course Acceptance – FCA).
- If you subsequently accept a place on a different course or on a course not offered to you through the CAO, you can submit a Course Change Notification Form at any time through the homepage of your online SUSI account.
Your application will be decided on the basis of the most recent course details provided to SUSI by any of the above methods.
Progression in Education and Repeating
In order to be eligible to receive a grant, you must progressing from year to year within your course or proceeding from one course to another leading to an award at a higher level.
With limited exceptions, you are not eligible for a grant if you are repeating a year of a course or if you are attending a course, or a year of a course, that is not deemed to be offering you progression in education.
Maximum Periods of Grant Funding
Maximum periods of grant funding apply to studies at each level. For further information on maximum periods of grant funding see www.susi.ie
Back to Education Allowance (BTEA), Vocational Training Opportunities Scheme (VTOS) and other Education Funding
You are not eligible to receive a maintenance grant if you are in receipt of BTEA or VTOS payments. You must inform SUSI if you are in receipt of these payments since, otherwise, you will be liable to repay any grant overpayment made to you.
You must also inform SUSI of any other financial assistance that you receive towards the cost of your maintenance as a student or towards your college fees.
This includes assistance by way of grants, bursaries, scholarships, etc. received from public funds provided by any Government department or other state-funded body and also includes assistance received from private sources.
Applications from within the Same Household
Each grant application is processed confidentially and separately, including where more than one application is received from within the same household.

This means that, where supporting documents are required, they must be requested and submitted separately in respect of each applicant within a household, even where the documentation in respect of two or more grant applicants within that household (e.g. siblings) relates to the same persons (e.g. parents).
Where applicants within the same household have consented in the making of their application to be cross-referenced with each other, SUSI may cross-reference grant applications for consistent and timely processing.
Relevant Persons in Education
Where certain persons relevant to you, the applicant, attend full-time courses of further or higher education in the same academic year, increased income limits apply that may deem you eligible to receive a grant or an improved rate of grant.
Contact Important Infomrs. Mac's Classes Nyc
You can provide initial details of such relevant person when submitting your online application and any grant you receive may be reviewed on this basis when further details of their attendance on a course is available.
Unless a relevant person is also a grant applicant who receives a grant from SUSI and has consented to having their application cross-referenced with your application for this purpose, you will be asked at the appropriate time to provide documentary evidence to confirm that they are registered and in attendance on their course.
Renewing Your Grant
You must apply online to SUSI annually to have your grant renewed for each year of the normal duration of your chosen course.
You can renew your grant ifyou are continuing on the same course (including where you progress from a “common entry” first year).
You cannot renew your grant ifyou change course or college (including where you enter an “add-on year” to a course) – in these cases you must make a new online grant application.
When renewing your grant, you must inform SUSI of any relevant changes in your circumstances that may affect your eligibility to receive a grant.
The renewal of your grant will be subject to reassessment by SUSI of your continued eligibility to receive a grant.
Deferring or Withdrawing
You must inform SUSI if:
- you defer a college place that you have accepted,
- you defer a year of your course, or
- you withdraw from or cease to attend your course.
If you do not inform SUSI promptly of this, you will be liable to repay any grant overpayment made to you and/or you may be ineligible to receive a grant (or may receive a reduced grant) on resuming your studies in the future.
11 Fraud and Error Control

SUSI implements controls to protect the expenditure of public funds, to prevent and detect fraudulent activity and to minimise errors in the processing of grant applications.
SUSI may cross-reference grant applications for audit purposes and for the detection and investigation of fraud.
Contact Important Infomrs. Mac's Classes Near
12 Privacy, Consent and Data Processing
SUSI respects individuals’ right to privacy and processes personal information securely and confidentially in accordance with data protection legislation.
SUSI may exchange personal data concerning you and other parties to your application with other Government bodies and agencies. This data is processed under agreed data sharing protocols for the purposes of verifying information provided in your application and confirming your registration and attendance at an approved institution.
Information on how SUSI processes personal data is provided in the SUSI Data Protection Statement.
When submitting a grant application, you and each other party to your application must individually confirm that you have read and understood the SUSI Data Protection Statement.
When confirming this, you and each other party to your application acknowledges the statutory basis under which SUSI processes personal data and also the legal basis for sharing it with other Government bodies and agencies.
Consent
As a grant applicant, your consent and the consent of other parties to your application, are not generally required for SUSI to process your personal data for the purposes of the statutory basis on which grant applications are received and processed. In circumstances where such consent may be required, SUSI will ensure that it is sought and freely given.
SUSI will not discuss personal data of a party to an application with other parties to the application, or with a third party outside the application without their authority.
Applicants and other parties to grant applications may also cross-authorise each other to discuss their personal data with SUSI on their behalf.
13.Further Information
Further information about student grant applications and awards is provided at www.susi.ie or you can contact our Student Support Desk at the addresses below.
SUSI – Student Universal Support Ireland, P.O. Box 869, Cork
SUSI – Tacaíocht Uilechoiteann do Mhic Léinn in Éirinn, P.O. Bosca 869, Corcaigh
Ph: 0761 08 7874
Email: support@susi.ie
Facebook: @Susisupport
Twiter: @Susihelpdesk
Website: www.susi.ie
Reviewed & updated April 2020
Home > Articles > Software Development & Management
␡- How Do Packets Get Around?
How Do Packets Get Around?
Up to this point, you have seen how to classify networks; you know that networks have an architectural type, topology, and protocols; and you know that networks are built to share information and resources. You also know that information is split into packets before being shared. This brings us to the next logical question: How do packets get from point A to point B?
To tackle this question, this section looks at two different examples:
A packet destined for a system on the same local network
A packet destined for a remote system on a different network
Before proceeding with these two delivery examples, let's take a minute to talk about the two most common protocols governing packet delivery: TCP and UDP.
Contact Important Infomrs. Mac's Classes 2020
TCP Versus UDP
The Transmission Control Protocol (TCP) and User Datagram Protocol (UDP) are protocols that run on top of the IP network protocol. Each has its advantages, but the key difference between the two protocols is the method of packet delivery and the guarantee of reliability and transmission.
UDP is a connectionless protocol that has very few error recovery services and no real guarantee of packet delivery. UDP is very much a 'fire and forget' protocol: You place packets on the network and hope they get there. For this reason, UDP is commonly used for network services that are not greatly affected by the occasional dropped or lost packet, such as network time requests and responses to name queries. In reality, the overall reliability of networks and data transmission makes UDP a good choice for many streaming network services. Because UDP is rather efficient, requiring no overhead for guaranteed delivery, it is becoming more popular with network application designers.
TCP is a connection-oriented protocol and is designed to allow two hosts to establish a reliable connection and exchange data. Contrary to UDP, TCP guarantees that packets will be delivered and processed in the same order in which they were sent. This guaranteed delivery is extremely important for many network applications, including such popular services as HTTP, FTP, and Telnet. To accomplish this, TCP uses a three-way handshake to establish connections:
The originating host (usually called the client) sends a SYN (synchronize) packet to the destination host (usually called the server). The SYN packet tells the server what port the client wants to connect to and the initial packet sequence number of the client.
The server sends a SYN/ACK packet back to the client. This SYN/ACK (synchronize/acknowledge) tells the client 'I received your request' and also contains the server's initial packet sequence number.
The client responds to the server with an ACK packet to complete the connection establishment process.
Figure 3.6 provides a graphical representation of the three-way handshake.
Figure 3.6 The TCP three-way handshake.
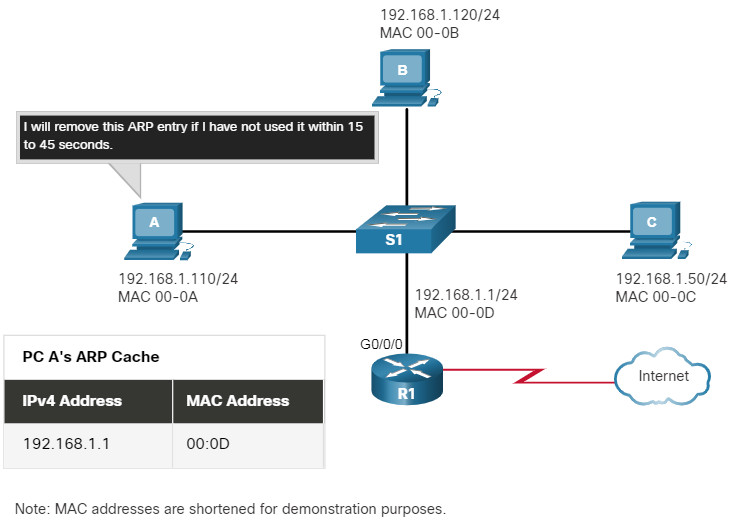
Local Packet Delivery
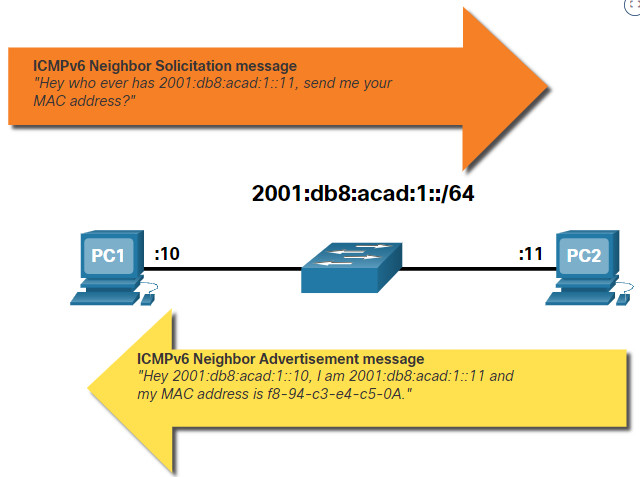
Now that you're familiar with the two main methods of packet transmission, assume you want to send a packet from your workstation to another workstation on the same Ethernet segment. The first step is fairly simple: you need to know the address of the remote workstation. From the discussion of IP packets, you know that the remote workstation's address is a 32-bit binary number. Since most people don't routinely remember 32-bit binary numbers, most applications let you use a dotted decimal representation of the destination address (in this case, assume your destination address is 10.10.10.101). Unfortunately, the IP address alone will not ensure your packet is received at the remote workstation. You have to find out the remote workstation's hardware address, the Media Access Control (MAC) address. MAC addresses are used to uniquely identify each node on the network and are usually hardwired into the physical network device, such as a network interface card (NIC), used to interface with the network media. In fact, at the lower layers of the Ethernet protocol, IP addresses are not even used. All network addresses are translated into MAC addresses.
To find a remote workstation's MAC address, the Address Resolution Protocol (ARP) is used. Basically, this is the computer's way of calling out, 'Who owns the tan minivan in the parking lot? (You have your lights on.)' Your workstation sends out an ARP request to find out, 'Who is 10.10.10.101?' Every node on the network will examine the packet, but only the workstation with the IP address of 10.10.10.101 will respond. It will send back an ARP reply to tell your workstation, 'I'm 10.10.10.101 and here's my MAC address.' Your workstation will then format the packet for delivery and drop it on the network media, stamped with the MAC address of the destination workstation. Ultimately, it is the MAC address that causes your packet to be received by the destination workstation.
Remote Packet Delivery
Local packet delivery is really not that difficult, but what if you want to exchange information with a remote system halfway around the world on a totally separate network? To illustrate, let's use a favorite pastime of most office workers: Web surfing. To get information, such as a Web request, to a remote server, you still need to know the remote system's IP address. In most cases you won't know the IP address of your favorite Web site, but you do know what the Web site is called. When you enter the name of your favorite Web site into your browser and hit Enter, the computer has to figure out where that Web site is and ultimately, that Web site's IP address. To accomplish this, your computer will use the domain name service (DNS).
DNS is basically a mechanism to translate names into IP addresses. Your computer will send a DNS query to a local DNS server (a machine whose main purpose is to respond to DNS queries) to find out, 'What's the IP address of this Web site?' The DNS server will then check its local records to see if it knows the IP address of the Web site. If it does, it will send a DNS reply to your system with the Web site's IP address. If it does not know the correct IP address for that Web site, it will query another, higher-level domain server, and so on until the correct IP address is returned.
When your computer gets back the correct IP address, it will look at the IP address to determine whether the remote system is on the same network. In most cases, the remote system is on another network that your workstation will not know how to reach. Your workstation will then create a packet, stamp it with the destination IP address, and forward the packet to the network gateway.
In many cases this gateway is a router. Routers are devices used to interconnect networks. Their job is to figure out how to move packets from one network to another. To accomplish this task, routers use forwarding tables to determine where a packet should go. When a packet reaches a router, it will look at the destination address to determine where to send the packet. If the router's forwarding tables know where the packet should go, the router will send the packet out along the appropriate route. If the router does not know where the destination network is, it will forward the packet to its defined gateway, which will repeat the same process. Eventually, after traversing various networks and being passed through various routers, the packet will come to the router serving the network with the Web site you are trying to reach. This router will determine the appropriate MAC address of the destination system and forward the packet accordingly.
For the average user, this entire process is completely transparent. The United States Postal Service serves as a good analogy. When you mail a letter, you put the appropriate address (including ZIP code) and a stamp on the letter before you drop it in a mailbox. The internal workings of the Postal Service takes care of the rest and the letter is delivered, usually without any further involvement on the part of the sender.
Subnetting
The remote packet delivery example is oversimplified, but you see how important IP addresses are to the packet delivery process. Let's take a minute to examine how an IP address is built. IP addresses really consist of two sections: the network section (prefix) and the host section. The network section of the IP address is usually referred to as the subnet, and the process of dividing IP addresses into networks is called subnetting.
Contact Important Infomrs. Mac's Classes Near Me
Look at the sample IP address from the local packet delivery example: 10.10.10.101. To determine how to split this address into the network and host portions you need to know the subnet mask. A subnet mask basically tells you how much of the IP address to consider the network portion and how much to consider the host potion. In practice, to determine the subnet this address belongs to, you perform a bitwise AND operation on the mask and the IP address. Here's an example:
First you must convert the address and subnet mask to their binary representations:
Then, by performing the bitwise AND you get the subnet address. The bitwise AND operation examines each set of matching bits from the binary representation of the subnet mask and the IP address. For each set where both the mask and address bits are 1, the result is a 1. Otherwise, if either bit is a 0, the result is a 0. So for this example you get:
The subnet address and mask both tell you that the first three parts of the address are network related, which means that the last part of the address is the host portion. In this example, the network portion of the address is 10.10.10 and the host portion is 101. Please bear in mind that this is a very simple example; subnets can get fairly complicated.
Subnets are usually divided in one of three classes:
Class A addresses, supporting 16 million hosts on each of 27 networks
Subnets: 0.0.0.0 to 127.255.255.255
Class B addresses, supporting 65,000 hosts on each of 16,000 networks
Subnets: 128.0.0.0 to 191.255.255.255
Class C addresses, supporting 254 hosts on each of 2,000,000 networks
Subnets: 192.0.0.0 to 223.255.255.255
Everything above 224.0.0.0 is reserved for either multicasting or future use.
In addition, certain subnets are reserved for private use and are not routed across public networks:
10.0.0.0 to 10.255.255.255
172.16.0.0 to 172.31.255.255
192.168.0.0 to 192.168.255.255
Finally, when determining the valid hosts that can be placed on a particular subnet, you have to keep in mind that the 'all 0s' address of the host portion is reserved for the network address and the 'all 1s' address of the host portion is reserved for the broadcast address of that particular subnet. Again from the earlier example:
In their forwarding tables, routers maintain lists of networks and the accompanying subnet mask. With these two pieces, the router can examine the destination address of each packet and then forward the packet on to the appropriate destination.
Assigning IP Addresses
There are two basic ways to assign an IP address to a specific device, such as a PC or server: the static method or Dynamic Host Configuration Protocol (DHCP). When you use the static method, you assign a specific IP address to a specific system. For example, 10.10.10.2 belongs to Jane's Linux workstation. No other system on that subnet can use that address; it belongs to Jane's system whether she is active on the network or not.
The second main method is DHCP, which is a dynamic addressing scheme that allows administrators to allocate IP addresses on a first come, first served basis. When a device configured to use DHCP (the client) tries to connect to the network, it will query for a DHCP server. The DHCP server will then provide the client with an IP address from a range of addresses allocated for DHCP use. These addresses cannot be used for any other purpose. Note that DHCP is an 'as available' protocol. If the server runs out of IP addresses, the next requesting client will not get an IP address and will be unable to connect to the network.
Another key feature of DHCP is the ability to limit the amount of time the client can use a particular IP address. When the DHCP server grants the client an IP address, it can also specify how long the client can use that particular IP address (sometimes called a DHCP lease). At the end of that lease period, the client must ask the DHCP server if it can continue using the same IP address or must attempt to obtain a new one.

DHCP can also make configuring individual network stations easier by specifying the default name server and gateway at the same time an IP address is assigned. There is little or no interaction on the part of the individual user. This lack of user involvement makes DHCP a very popular choice for large corporate networks and Internet service providers (ISPs). Most ISPs, whether they are dial-up or broadband, use DHCP to configure user connections.
Routing
The overall process of delivering a packet from point A to point B is usually referred to as routing, and the devices primarily responsible for accomplishing this task are usually called routers. Essentially, it is a router's job to know where the packet needs to go next. You already know that routers use forwarding or routing tables to determine where to send a particular packet based on destination address. But how do routers build their routing tables?
There are a number of different ways to build routing tables, and different routing protocols have been developed to assist in the creation and maintenance of routing tables. Sharepoint sync app macnewpb. Some of the more common protocols include
Static—Routing entries are entered once and are not updated again. Static routes are often used to define the last resort next hop. If you don't know what else to do with a packet, send it here. In some ways, static routes are more secure than other routing protocols because there is less danger of a malicious individual attempting to reroute your network traffic by manipulating your routing tables.
Routing Information Protocol (RIP)—Entire routing tables are shared between routers on a periodic basis. This is a rather inefficient and insecure way of sharing routing information.
Open Shortest Path First (OSPF)—The shortest and most efficient route to reach a particular destination is calculated based upon the path that must be traversed, the state of the links that must be followed, and the nodes the traffic must pass through. Although efficient in traffic delivery, this method requires a great deal of overhead.
Border Gateway Protocol (BGP)—Peer routers called neighbors exchange routing information between autonomous systems. Although initially entire routing tables are exchanged, following exchanges are limited to updates and keep alive messages only. BGP is designed to ensure a loop-free route to the destination network.
Related Resources
There are currently no related titles. Please check back later.
